Herstmonceux Castle and Moat for TO6410 cc Dave Croker
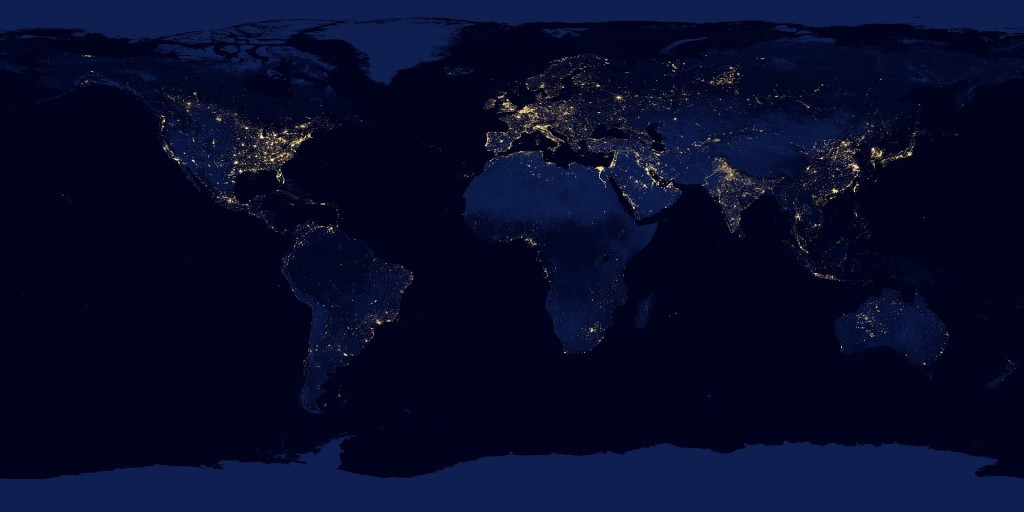
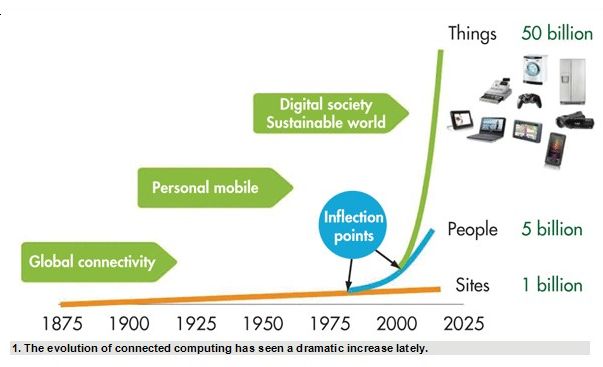
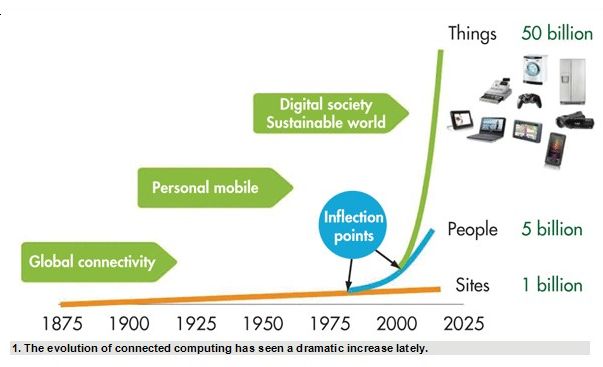
Planners who were trying to safeguard valuables back in the middle ages discovered that it takes more than fortifications to succeed. This is especially true when the fortifications have secret doors that were installed by the builder. I suspect that the fortress defenders discovered that the addition of a moat also flooded the tunnels under the walls. In this digital age, the task of defending a company’s digital fortress is daunting. The magnitude of this task will only increase as more of our foreign-built devices become internet connected.
by Stan Schneider Real Time Devices
As revelations by Edward Snowden and others have demonstrated, the fortress walls of these IoT (Internet of Things) devices come with pre-installed secret doors. This fact has not escaped the thieves that exploit these weaknesses. In much the same way that Google crawls the web looking for home pages, a search engine named Shodan crawls the web looking for the hidden back doors
http://www.forbes.com/sites/kashmirhill/2013/09/04/shodan-terrifying-search-engine/. Using this search engine to help them, I am not surprised that the thieves find that some of these doors are unlocked. So how do you go about installing a moat before the thieves make off with the crown jewels? What does a modern moat look like? The first moat of the electrical age was related to the high voltage wires needed to transmit power for long distance. Nickolai Tesla working for George Westinghouse developed the high voltage power system we use today. Glass insulators kept the high voltage from shorting to ground.

Sophisticated insulators stop the loss of high voltage power
It is very exciting when the salt we use on the road causes massive fires in the substations melting the conductors. Obviously the fuses blow, but most of us have also lost a TV, radio or computer because the high voltage finds its way into our electronics. The fragile electronics in our computer chips died regularly, until we discovered how to use light in the form of opto isolators to build a non-conducting moat around the processor.

light waves protect microprocessors from voltage spikes by Inductiveload
Light can also be used to protect the program running the computer from hacking and malware. Early in the development of microelectronics a type of memory called UVprom was invented. Bright ultraviolet light bathed on the chip erases the memory.

Ultraviolet light erases this chip CC by SA 2.5 ST Microelectronics M27C2568-12FI
The convenience of the electrically erasable chip has led to its wider use. In general, it is not convenient if spyware and malware are remotely added using the electrically erasable chip to steal the crown jewels. I suspect that the vandals of the middle ages would have liked conducting their raids without ever having to leave home. I believe that we will go back to locking in the operating program. It is promising to hear that Google is unveiling their Vault micro SIM card for a mobile phones. We will all be watching to see whether it actually improves security or is just to keep out every one but Google (and the NSA by hidden deal)
http://www.cnet.com/news/googles-project-vault-is-a-security-chip-disguised-as-an-micro-sd-card/ This is probably why so many users cling to Windows XP (also named Windows NT) Daily web updates to fix the bugs in incomplete operating systems are a big gap in the moat we are trying to build around our data fortress.
In the early days of computing, many of us used time sharing. The derivative virtual machine adds one more level of security but it does not protect against back doors that were embedded in the parent operating system.
Virtual Marble Machine CC by Torley
I like playing video games, but if I am interested in data security I will go back to build and maintaining the moat. Windows NT is very stable and bug free operating system if is isolated from the web. Thinking in military terms it is better to have a mine field between you and the theives. We have all played minesweeper.
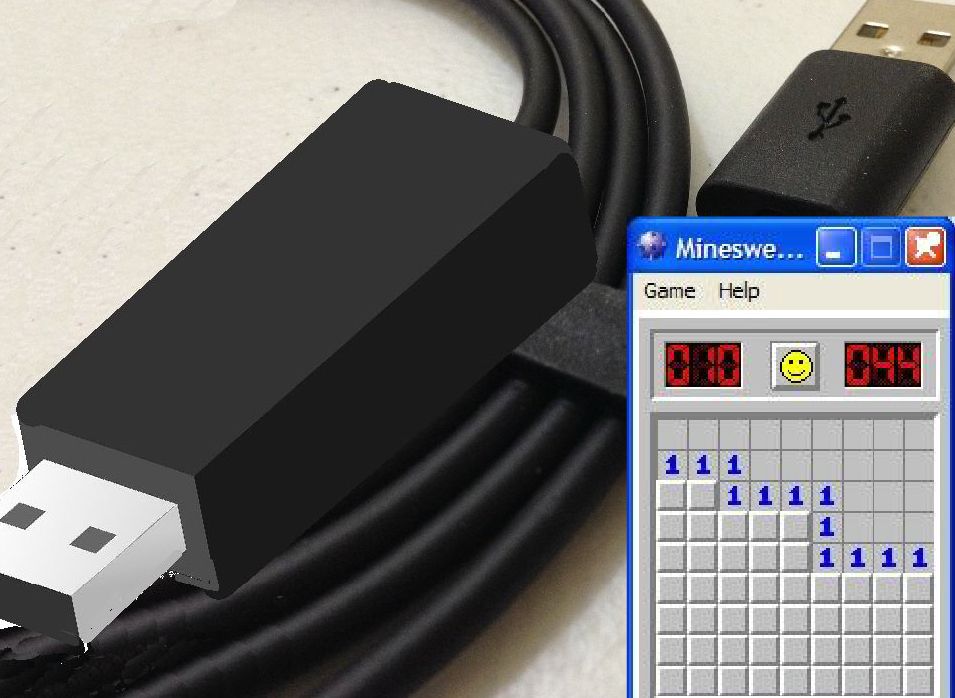
Memory with embedded “mines” can be built into the cables that connect to the internet
Remote probing is a lot more difficult if only a small amount of data is availaible at one time in a two directional buffer memory and random memory addressed are mined.
Currently 40% of the cost of new vehicles is software. Companies who wish to remain in business must take building a moat against the “Great Cannon of China” more seriously